Trisul Blog
From platform-wide 2FA and MITRE ATT&CK integration to Trisul AI and NetBox-powered IPAM, Trisul is building toward faster investigations and smarter analytics.
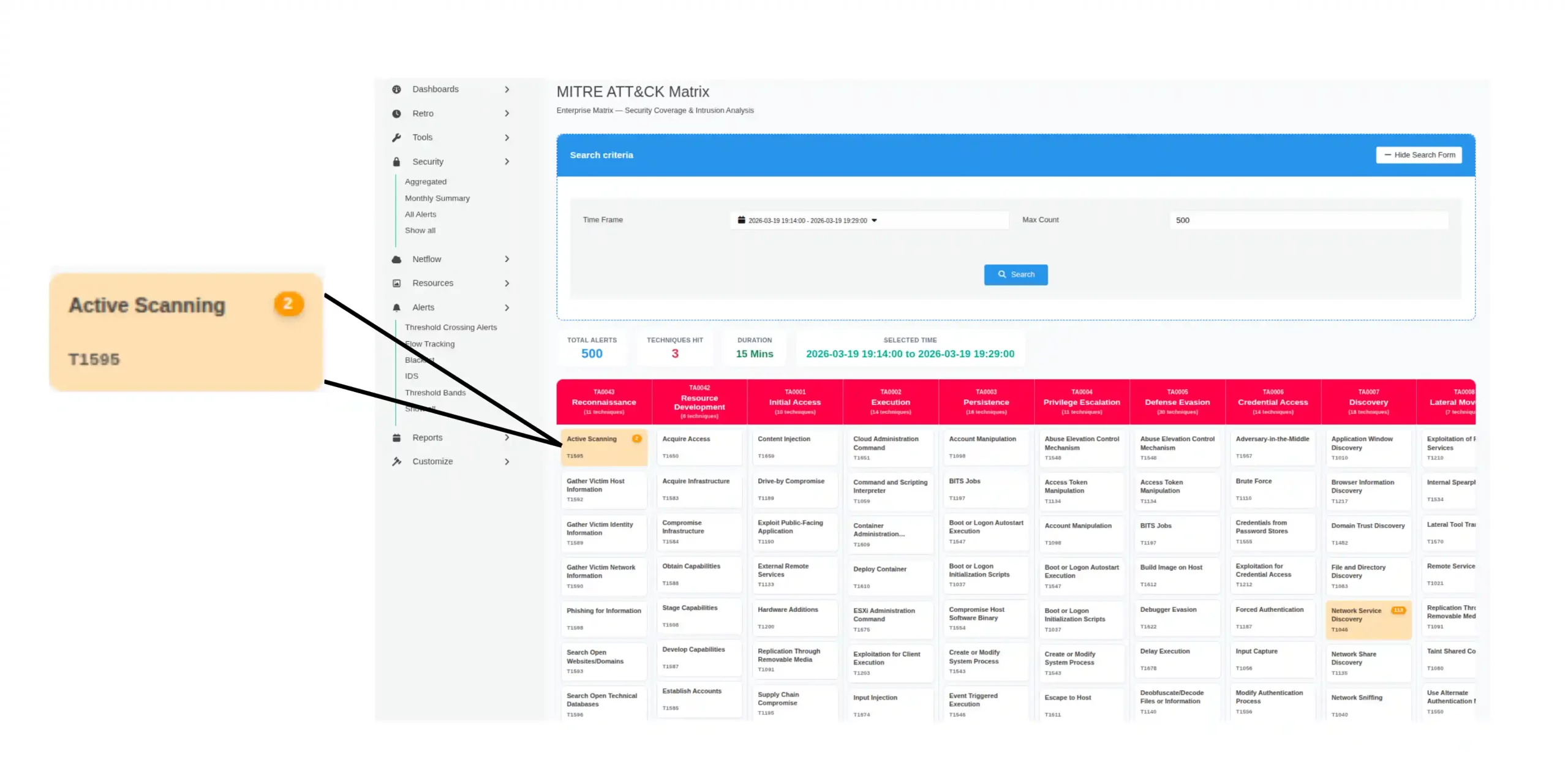
Security alerts often appear as isolated events, making it difficult to understand whether they are part of an attack. In this article we explore how Trisul maps network detections to MITRE ATT&CK tactics and techniques, adding behavioral context to alerts and visualizing activity directly within the ATT&CK matrix.
Modern IPDR compliance is no longer a background configuration. It’s an operational capability that must keep pace with evolving network complexity.
AI is entering IPDR compliance, but not in the way you might expect. Trisul uses AI as a secure bridge between people and compliance workflows, helping teams move from request to report faster while keeping sensitive data protected and processes unchanged.
A look back at 2025 through the lens of system behavior, investigation flow, and how Trisul made intelligence more reachable without changing its foundations.
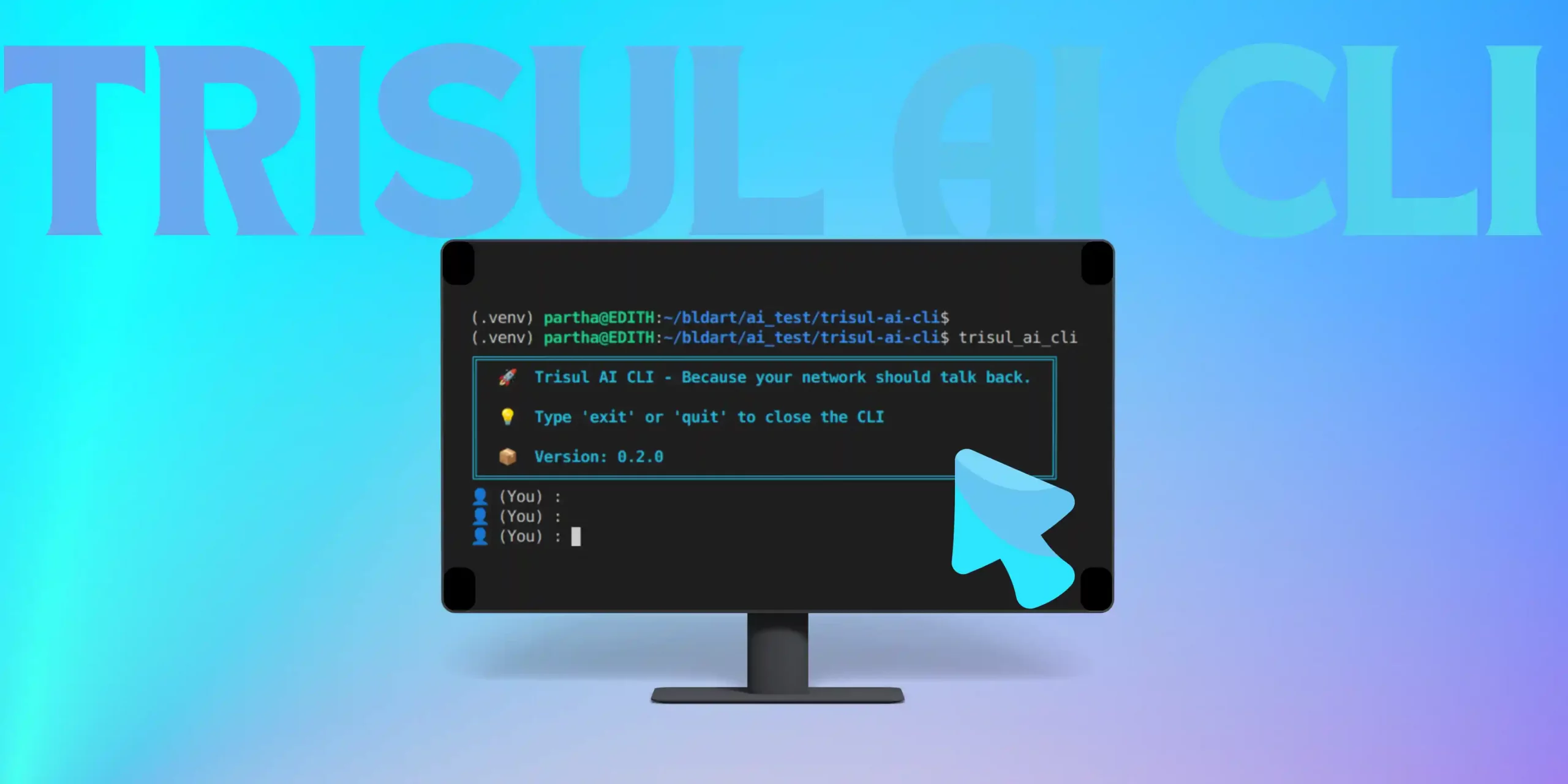
What happens when AI stops explaining dashboards and starts working with live network data? Trisul AI CLI explores that shift in production environments.
Scattered logs, endless dashboards, reports everywhere, ugh! Trisul AI swoops in like a superhero, turning all that chaos into instant, actionable, conversational insights connecting the dots. Just ask, and get answers fast and accurate!
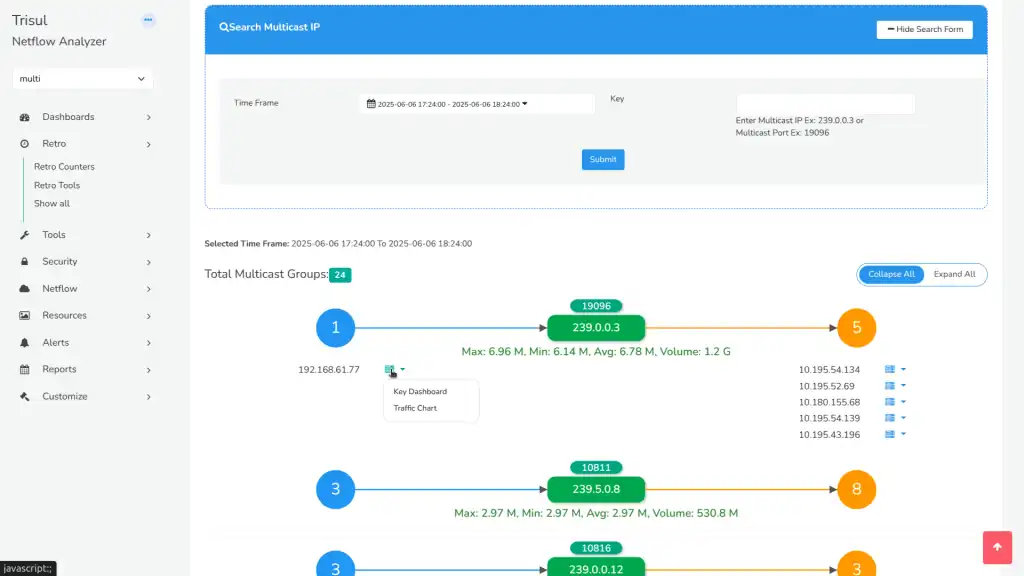
This release is all about speed, clarity, and control. From visualizing multicast flows with GraphX to faster bulk IPDR queries, regex-powered key monitoring, and smarter utilization alerts. Trisul delivers features you’ve been asking for, designed to cut noise and surface what matters.
From missing NAT logs to silent storage failures, one overlooked detail can derail months of IPDR compliance work. Here’s how ISPs can stay audit-ready without burning out.
Multicast traffic has long been a black box in network visibility. With Multicast GraphX, Trisul gives you an interactive visual map of multicast groups, senders, receivers, multicast traffic metrics.