TRISUL NETWORK ANALYTICS
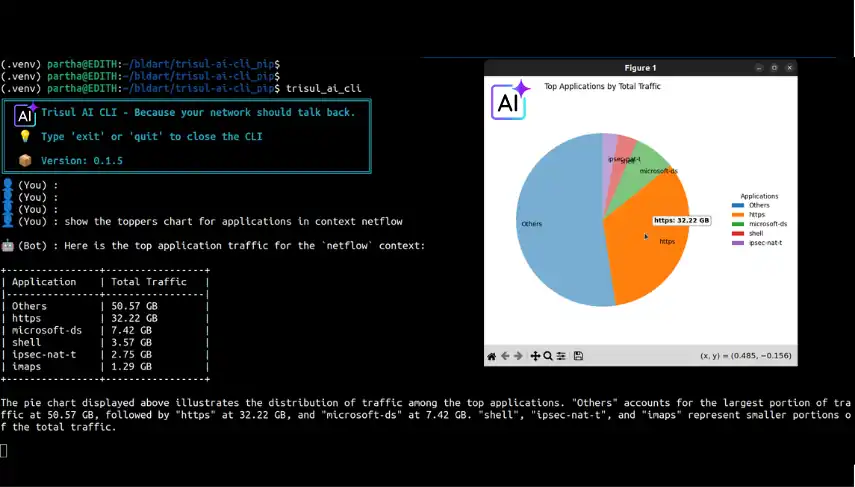
AI-Assisted NetFlow and Packet Analytics for Deep Network Visibility
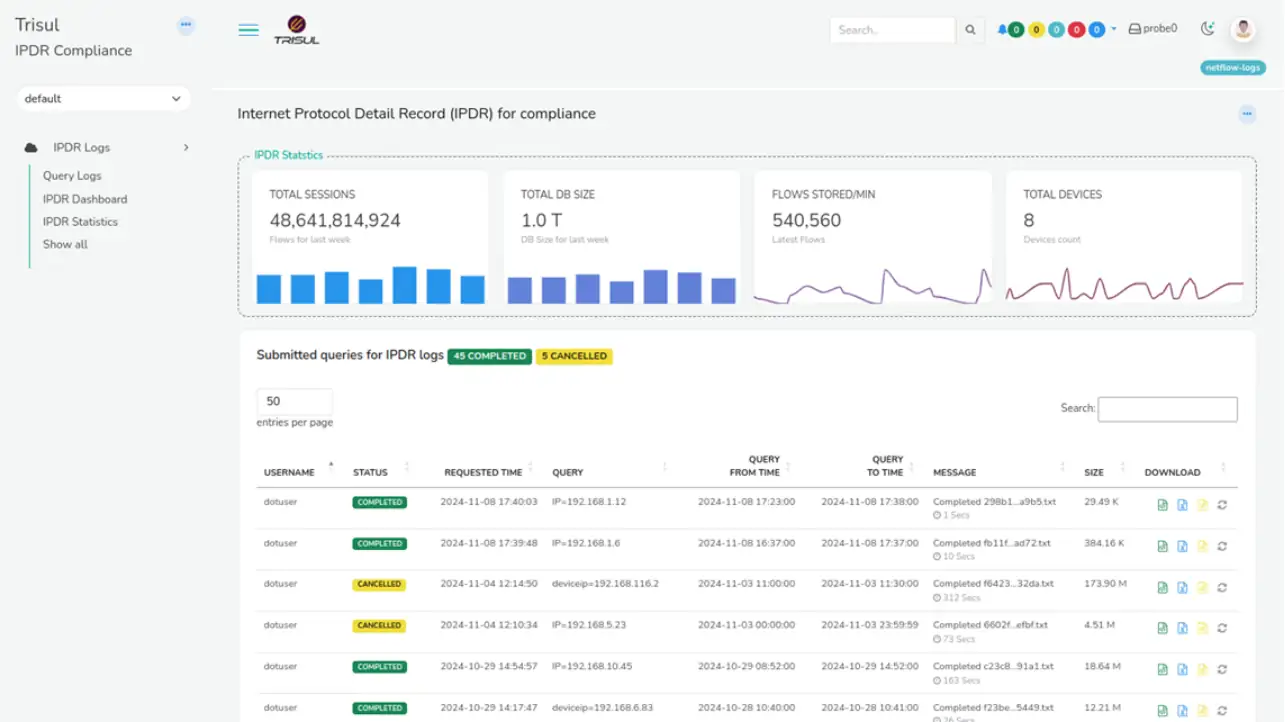
Analyze NetFlow, packets, BGP, SNMP, and Syslog in one platform to detect anomalies, investigate incidents faster, and generate audit-ready network data without switching tools.
Network Traffic Monitoring for Security & Compliance
For ISPs · Security Teams · Enterprise Networks
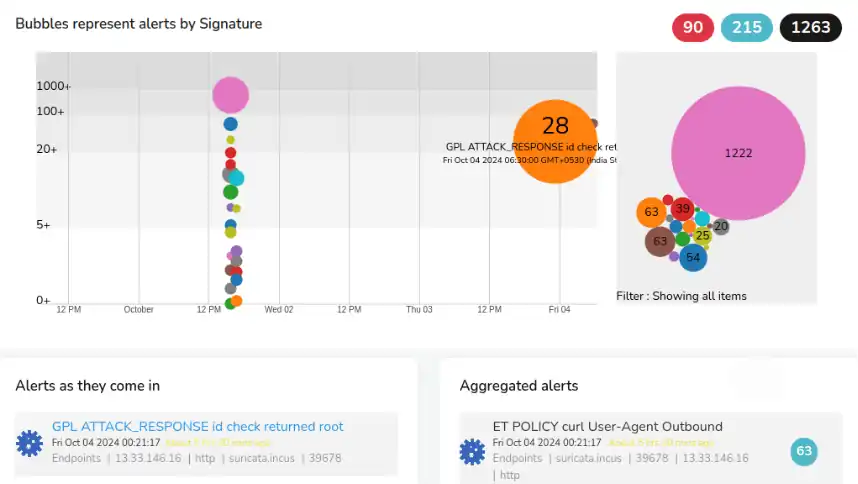
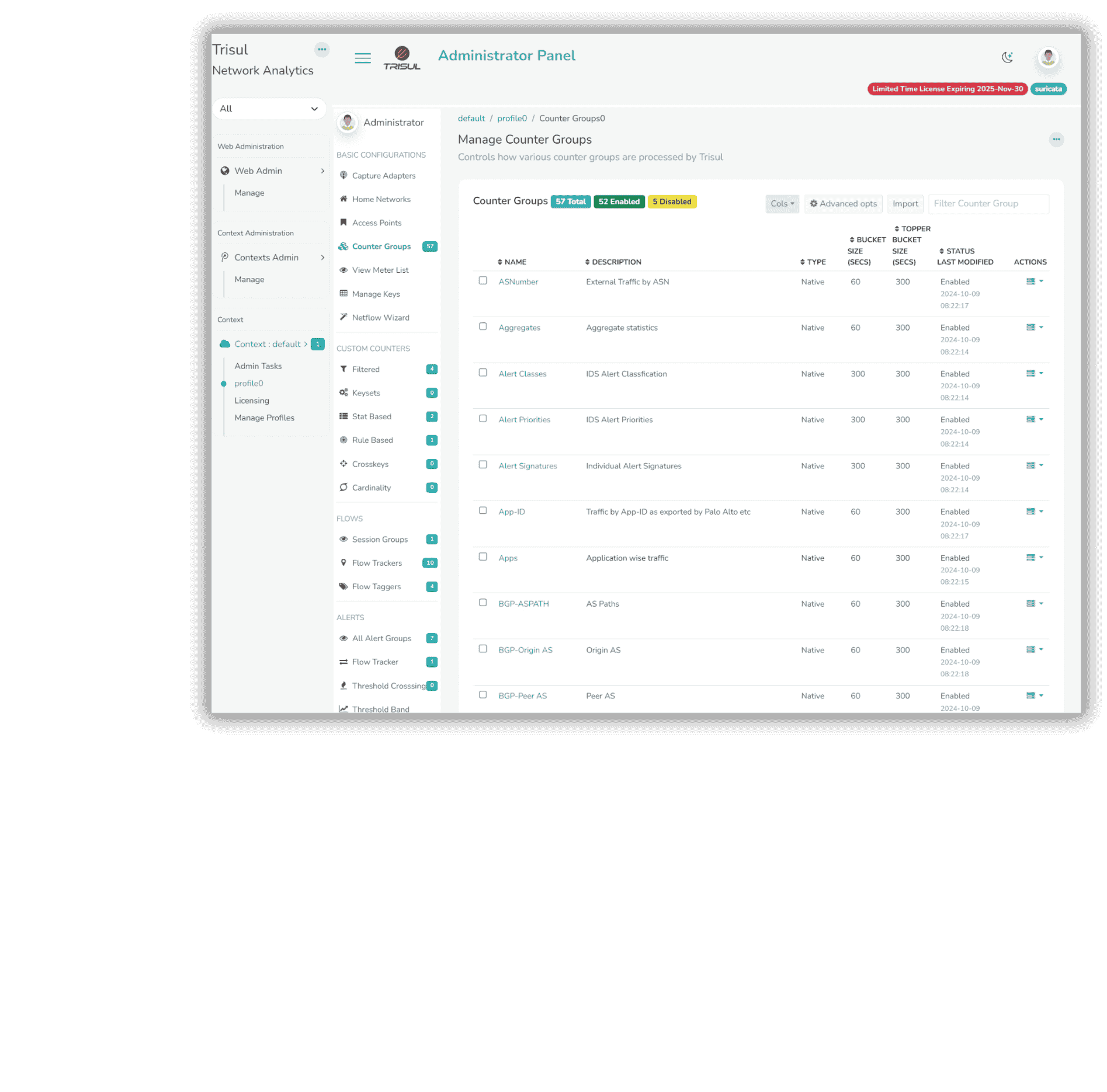
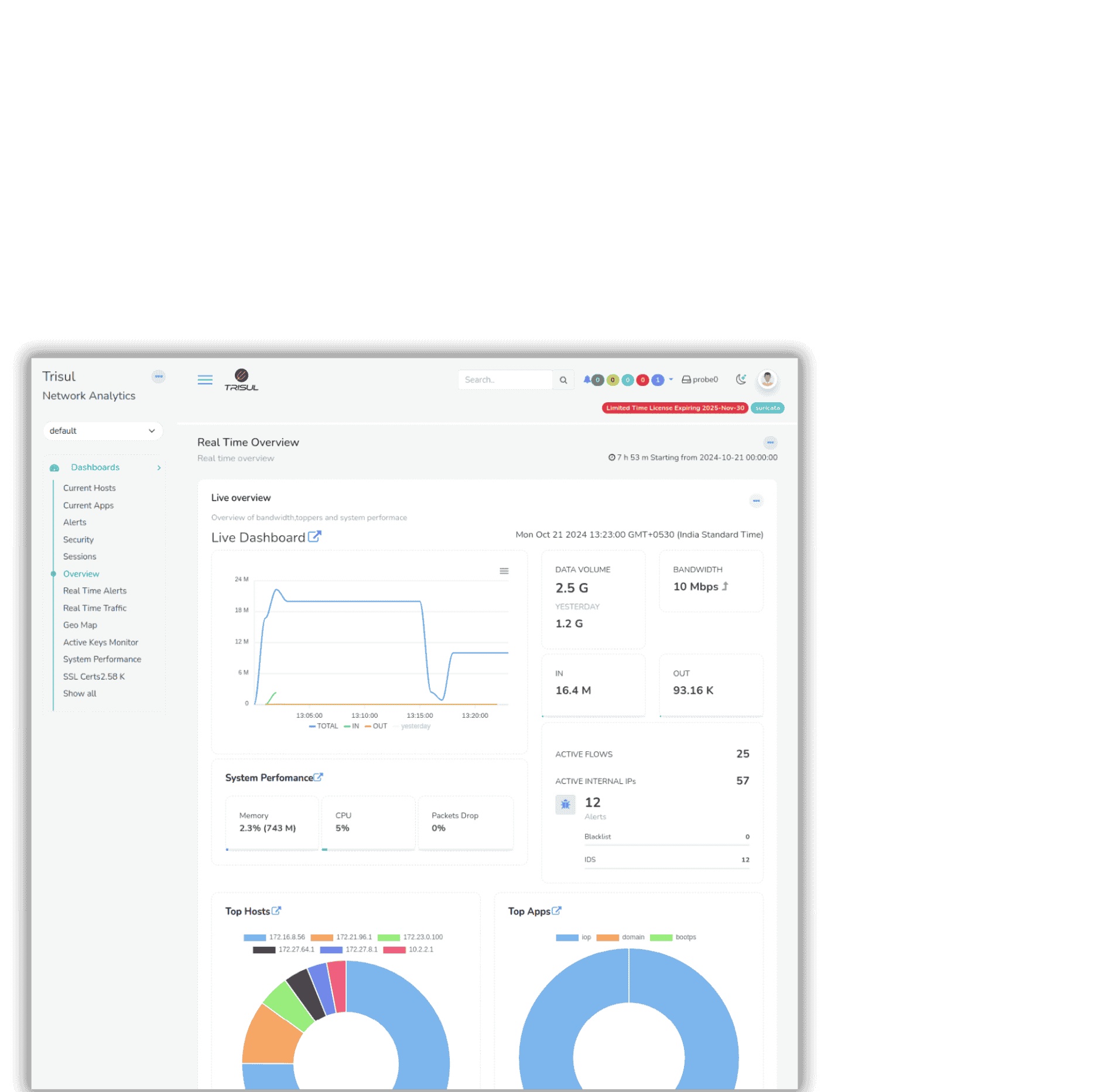
Deep Metrics for Real-Time Network Visibility
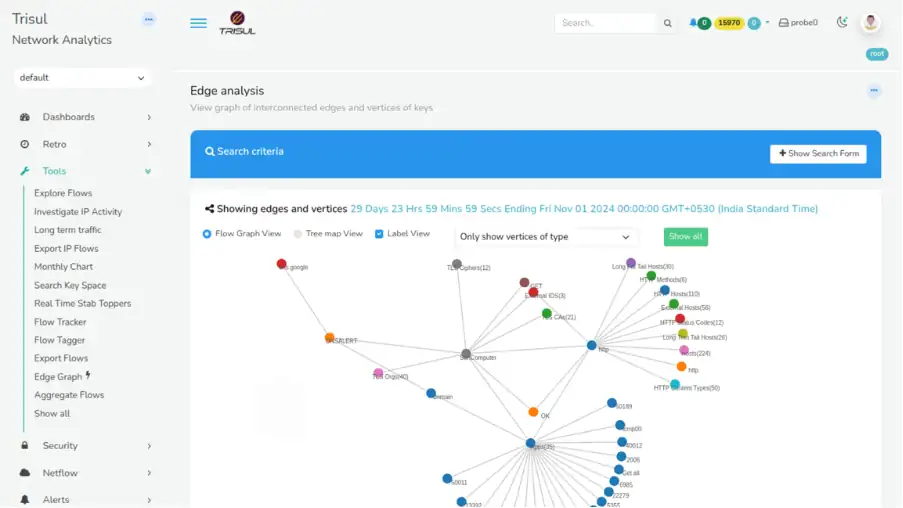
Gain full visibility into network performance with deep metrics across applications, hosts, TLS, Ethernet, and geo data. Combine this with flow analysis and graph-based insights to detect anomalies early and investigate issues in real time.
- Analyze millions of metrics across network, application, and infrastructure layers in real time.
- Built-in algorithms: Top-K, Bottom-K, cardinality, and first-seen detection
- Perform retrospective analysis for faster incident response
- Ingest packets, NetFlow, SNMP, and logs in a single platform
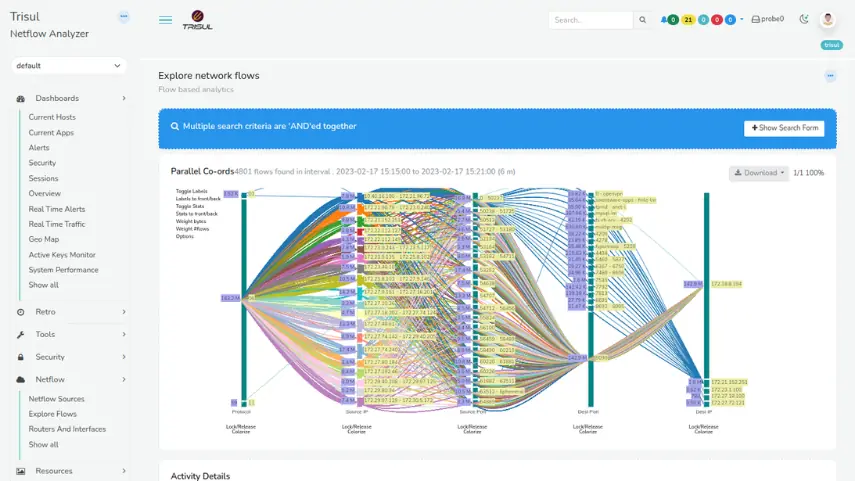
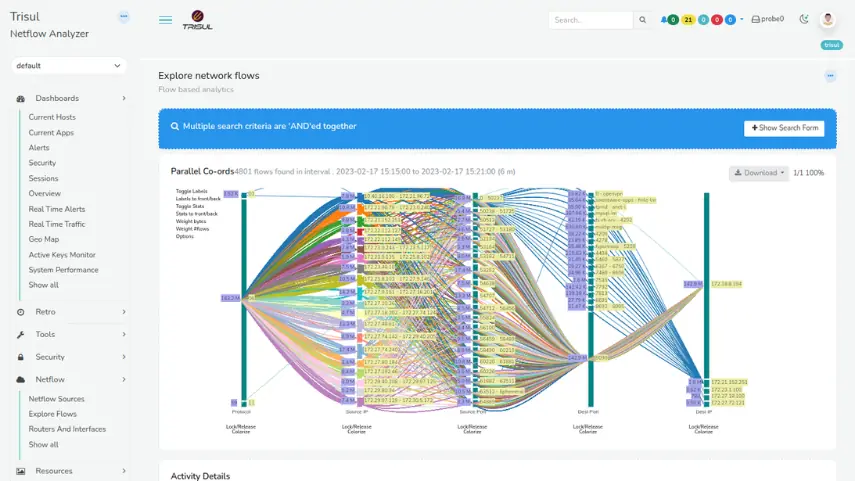
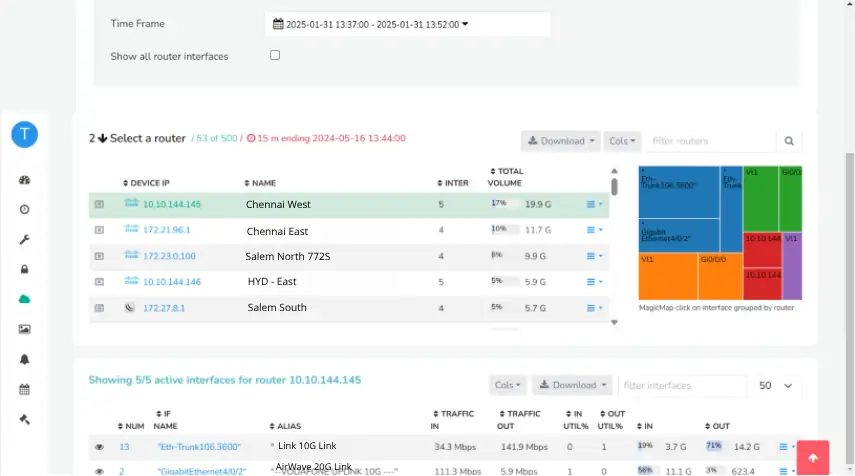
Capture and Analyze Every Network Flow in Real Time
Track every network flow across your infrastructure without sampling, summarization, or data loss. Capture every network flow without sampling to enable accurate investigation and forensics.
- Ingest NetFlow, sFlow, IPFIX, or reconstruct flows directly from packets
- Query flow data with a flexible, high-performance search language
- Add context with Flow Taggers for faster filtering and investigation
- Store complete flow records with no rollups or data reduction













HERE'S EXACTLY WHY YOU NEED TRISUL

Start Monitoring Network Traffic in Minutes
Try Trisul with a full-featured three– day 7-day trial. Analyze NetFlow, packets, and PCAP data in real time without sampling or limitations. Deploy instantly using our Docker image on Linux and start gaining complete network visibility.
No Credit Card Required.



