Announcing the IOC Intel Harvestor App
The Trisul NSM platform has always provided a way to integrate threat intelligence feeds using the Badfellas Plugin. That works great but it is limited in flexibilty. The Trisul LUA API lets you gain total control over the process of harvesting intel pieces and performing the checks.
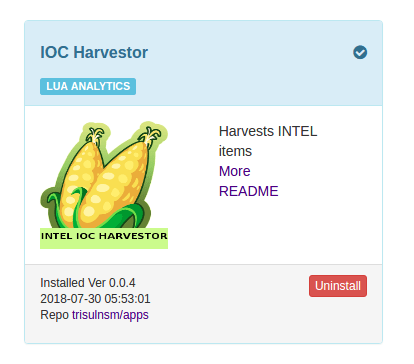
We just released a new Trisul APP called Intel IOC Harvestor that lets you trivially build advanced capabilites. This blog post describes this new APP.

The Intel Harvestor APP currently pulls out 14 different types of IOC Intel including IP addresses, Domains, SSL Cert hashes, File hashes, TLS SNI, SAN, JA3, and others.
How the IOC Intel Harvestor App works
In Trisul LUA Scripting, you write LUA scripts that plugin to various streams, and then process pieces of information as they fly by. Without the new IOC Harvestor APP you would have to write small scripts for 14 different streams. The IOC Harvestor APP just does this work for you. See the figure below , on the left side you see a number of streams in Trisul, this APP pulls out all of this into a single stream.

With the IOC Harvestor APP installed you get a brand new Resource Stream called “Intel Harvested”. Then you can just write a function that processes each INTEL artifact as it flies by.
Example integration
After installing the IOC Harvestor APP, you can put the following code in a file , say test1.lua and it will print all the INTEL items to stdout. You can see how clean and simple the user interface is.
TrisulPlugin = {
id = {
name = "Intel Harvest Tester",
description = "Dump the INTEL to stdout",
},
resource_monitor = {
-- this is the GUID for the Harvested-Intel resource group
resource_guid = '{EE1C9F46-0542-4A7E-4C6A-55E2C4689419}',
onflush = function(engine, resource)
print(" Here is IOC INTEL Harvested type="..resource:uri() .. " value="..resource:label())
end,
},
}Plugging this into a threat intel feed like Alienvault OTX
A full threat intelligence on a Network Security Monitoring platform consists of two components.
- Part-1 Harvesting from network traffic – The Intel IOC Harvestor app described in this blog provides this piece.
- Part-2 Checking with Threat Intel – Process threat feeds like Alienvault OTX, CriticalStack into a format that allows us to check in real time.
There are a number of ways you can do Part-2 using the Trisul LUA API. For example you can load the entire INTEL list into memory like we do for the FireHOL checker APP This is easy for small lists which wont take up much memory.
What we recommend is to stuff all your INTEL into a LevelDB database and then use the TrisuL LUA API to simply check the DB for a hit.
Take a look at our AlienVault OTX LUA Script on Github This includes a Ruby script that connects to OTX , downloads the intel pieces, and stuffs it into a LevelDB database. Then we have a very simple script that just scans all harvested items against the LevelDB database.
You can of course use your own method instead of LevelDB, it is just plain LUA. That is the flexibility of the Trisul Network Analytics API.
Trisul Apps are available even to those using the Free License. Do try them out.

Free Download Trisul 6.5 ! Ready to go packages for Ubuntu and CentOS.