Release 3.0 Maintenance Updates
Hey Trisul users, we’ve got a maintenance update to Trisul 3.0.
Fixes and enhancements
- Fixed a Memory leak in Payload Search for file MD5
- Fixed a bug when TCP Sequence numbers wrap more than 1 time
- Other minor tweaks
We’ve also added a new option in Tools → Payload Search based on a real world scenario. We’re sure you will like the possibilities that this feature offers.
New ! Payload Search only first 1MB of each flow
Presently the “Payload Search” feature reassembles entire flows looking for patterns. This is wasteful for some key use cases as we found out as a lot of the action we look for happens towards the beginning of the flow. So we added a new button to only look for stuff in the first 1MB of each flow.
I want to share a couple of interesting scenarios with you.
- SSH/SFTP running on non standard ports
- File types being transmitted in the clear
Payload Search for SSH on non standard ports
Per RFC 4419 SSH clients and servers exhange string patterns representing the diffie hellman group and encryption methods supported. Searching for diffie-hellman-group-exchange-sha256,diffie-hellman-group-exchange-sha1 in the first 1MB of each flow will pick up all the SSH based services in use.

Fig: You only need to reassemble & search the 1st 1MB
Payload Search for file types
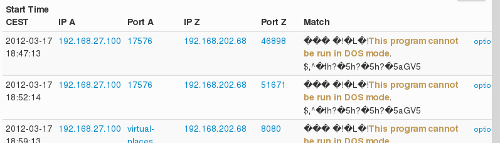
Looking for the classic “This program cannot be run in DOS mode” can pick up quite a bit of Windows EXE malware and supporting software being ferried across. Another way would be use the Resources → HTTP Header FTS to search for Content-Type: application/exe but that can be faked. This is the real deal !!

Fig: Simple way to pick out some Windows EXEs
Enjoy the new update folks !

Download Trisul today. Dont just monitor, start NSM-ming !