Trisul NetFlow Analyzer 2024- Going Above and Beyond in Network Traffic Analytics
Data analytics has become the primary driver of business strategies and potential for all industries to make data-driven decisions. However, not all data analysis tools are built equal. In this article, we will explore how Trisul NetFlow Analyzer innovates to differentiate itself from traditional flow-based monitoring approaches to deliver maximum benefit to businesses in a constantly evolving network traffic technological world.
Why Is The Role of NetFlow Analyzer So Important in 2024 ?
The pyramid of network traffic analytics shows the levels of monitoring techniques from the basic connectivity status (PING) at the bottom to the advanced, high-level technique Deep Packet Inspection (DPI) at the top, offering comprehensive insights into network traffic and application behavior. NetFlow provides the most effective sweet spot in 2024 for traffic analytics.
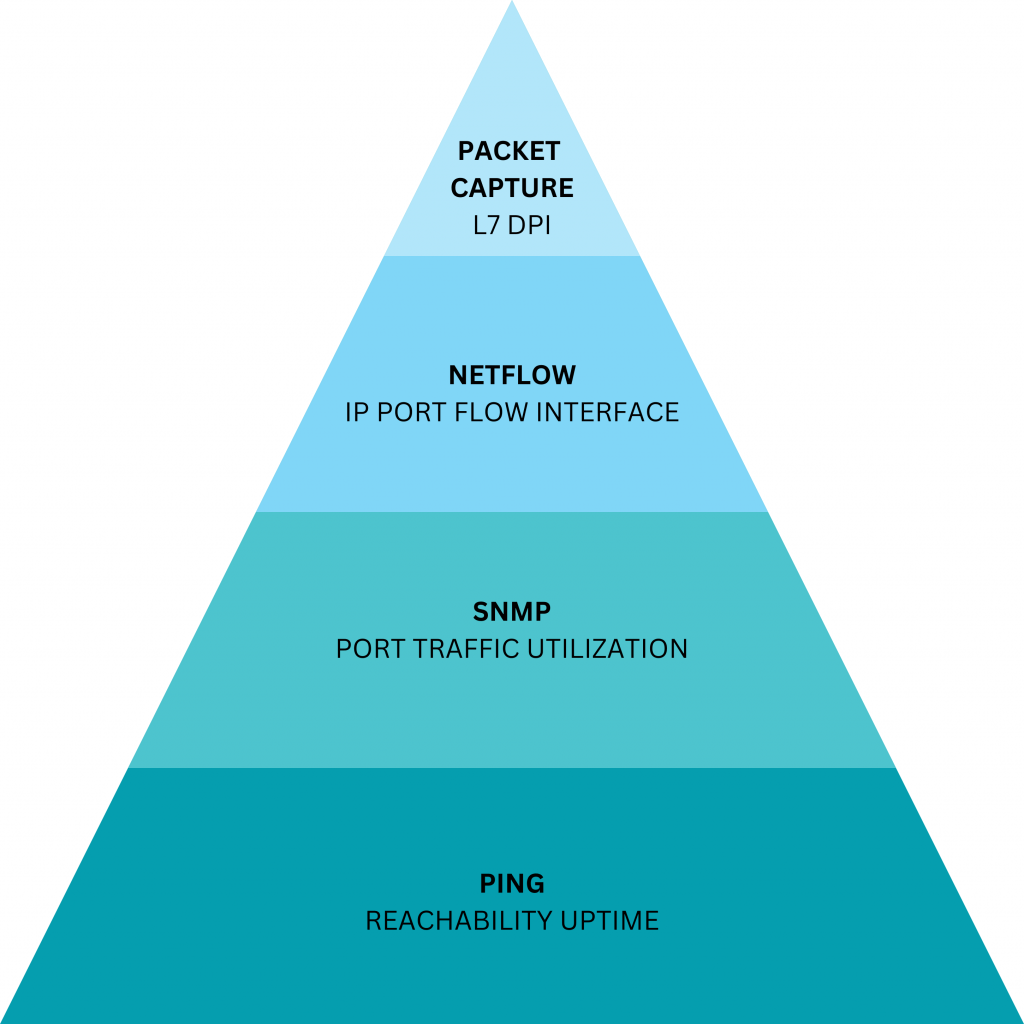
NetFlow technology is ubiquitous, almost all your routers, switches, and firewalls have it. You would be wasting such a precious feature that is provided for free if you do not exploit its potential. The darling of the 2000 and 2010s was “Deep Packet Inspection” or DPI this is shown as the apex of the pyramid. However, these days in 2024 DPI is severely hobbled by the pervasive use of end-to-end encryption which for all practical purposes prevents seeing any packet contents beyond the headers. In contrast, NetFlow support keeps improving as SD-WAN, Firewall and Router vendors add more metadata fields such as User-ID and App-ID. All devices export NetFlow packets to a NetFlow Analyzer, but the features and technology used by the NetFlow Analyzer make all the difference.
Full suite ITSM solution providers focus on IT-oriented network tools and only offer basic traffic monitoring capabilities in their NetFlow product. The Trisul Network Analytics platform is purpose built for network traffic analysis, it has three flavors depending on the algorithms and database used.
-
-
- Trisul NetFlow Analyzer: Specifically built for deep visibility and detection
-
- Trisul ISP Edition: NetFlow, BGP, DNS, and SNMP combined for peering, prefix, and route analytics
- Trisul IPDR: Flow logging compliance
-
The Trisul NetFlow Analyzer Difference – Streaming Analytics
Once installed, Trisul captures and analyses high-speed flow data generated by network devices such as routers, switches, or firewalls. These flow records contain key information including source and destination IP addresses, source and destination ports, protocol type, type of service, and timestamps. While traditional NetFlow analyzers store these flow records into a database for further querying, Trisul NetFlow analyzer uses streaming analytics to process flow data as it gets generated and analyses them in real-time. Think of it as always-on queries that work on real time data and snapshot their results every window. Streaming analytics help you answer questions that can be extremely difficult for traditional approaches. Let us consider an example.
An Example of Streaming Analytics
Say you want to ask the following question
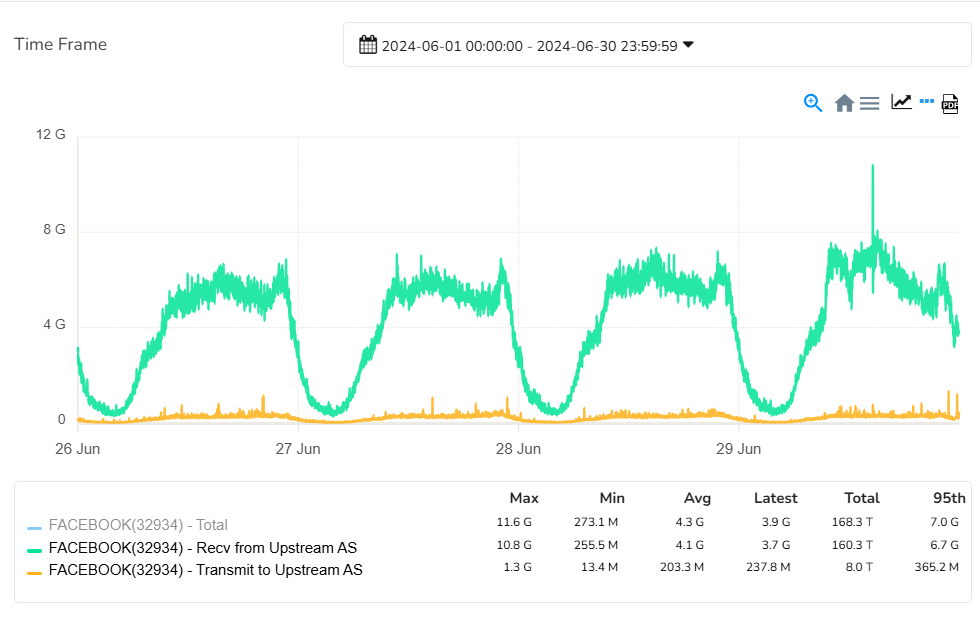
Show me the traffic chart receive and transmit to Facebook on my WAN1 interface for the month of June 2024
The traditional database approach is to query the flow database with the “where ASN = FB and Time = June 2024”. The image below illustrates the two records that match.
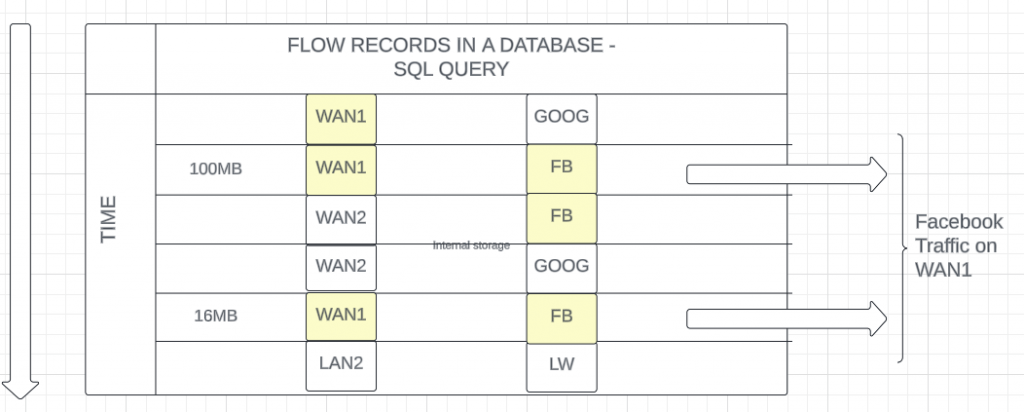
This simple approach however has several problems. First, you need to scan the entire flow dataset for June 2024. That itself is prohibitive in most cases. Second, you lose the temporal (time series) characteristic because flows only store the total volumes. This is why this type of query isn’t provided by many simple NetFlow analyzers.
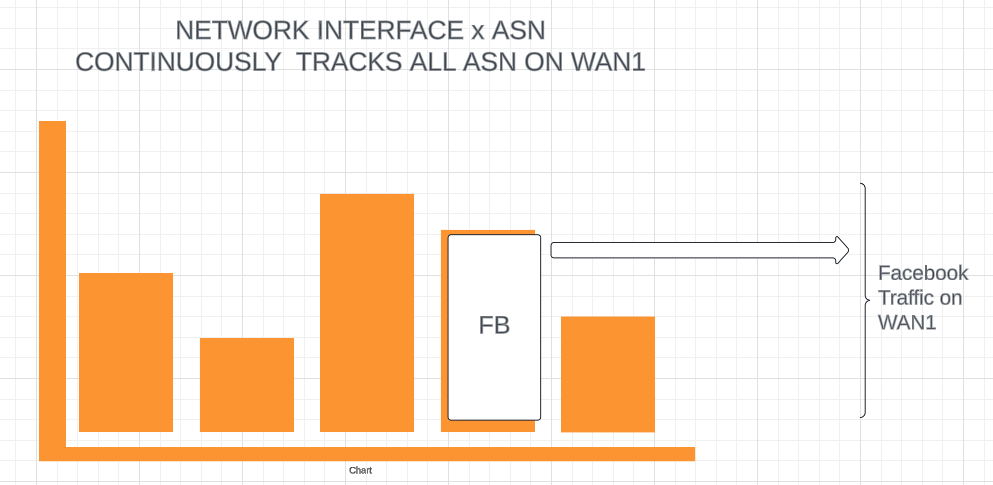
By contrast, Trisul uses a streaming analytics algorithm called CrossKeys to snapshot the Network Interface x ASN cross product every streaming window, which is every minute. Therefore the query is already precomputed. You can just go to the right place and return the results even for 1 year.
Other Advantages of Real-Time Streaming Analytics
Streaming analytics has other advantage above and beyond the timeseries example described above. A few of the unique features available in Trisul NetFlow Analyzer are
-
-
- Enrichment: Enhancing flow records in real time by Geo data, flow tags, alert marks and so forth
-
- Top Talkers in Real Time: See the top talkers on an interface in real time even before they are stored in the database.
-
- Alerting: Use threat intelligence to flag malicious traffic as they are received in real time. Also to alert on traffic anomalies such as DDoS and to pinpoint which IP addresses are involved.
-
- Flow tracking: Track in real time flows uploading large file attachments or other suspicious behavior.
- Segmentation: Split the real time stream into substreams ; example only monitor applications on a specific subnet for example.
-
In summary, the analysis process involves identifying patterns and trends in network traffic as they occur, detecting unusual or suspicious activities in real-time, and continuously monitoring performance metrics including bandwidth usage and latency. The most common use cases of organizations such as identifying which users, applications, protocols, countries, AS numbers, top routers, and top interfaces are consuming the most bandwidth is easily available. Streaming algorithms help take each of these use cases to the next level.
Challenges with Traditional NetFlow Analyzers
Traditional NetFlow analyzers or legacy monitoring solutions face several challenges that impact their effectiveness in modern network environments. Some Key challenges include,
Compatibility
Different equipment vendors like Cisco, Juniper, Huawei, Palo Alto, and Fortinet that offer routers, switches, and firewalls implement NetFlow or IPFIX in slightly different ways leading to compatibility issues. Also, NetFlow and IPFIX have evolved over time with different versions offering varying features and capabilities so each version may not be supportive with every device. Some devices may support basic flow data while the enterprise’s use case may require additional information such as QoS (Quality of Service) metrics or application-level details.
Resource Intensive
In large-scale deployments or networks with high traffic volume, NetFlow data accumulates rapidly. Processing and analyzing such a high volume of data require substantial computational resources, especially in terms of CPU processing power and memory capacity. Furthermore, storing flow records for compliance or historical analysis that might need to be retained for extended periods to analyze long-term trends, patterns, and anomalies requires adequate storage infrastructure.
Complexity
In large networks, a wide variety of network devices from different vendors are spread across multiple locations. Configuring a NetFlow Analyzer in such large, distributed networks often consists of complex topologies with interconnected network segments, remote offices, and branches. It is challenging to capture flow data from all appropriate network segments while maintaining global visibility across the entire network.
Real-Time Limitations
Basic NetFlow analyzers struggle with real-time processing of flow data, leading to unavailability of upto the second views of current traffic conditions that are crucial for network troubleshooting, delayed detection of modern threats and response to security incidents. The processing speed of legacy tools may not keep up with high-velocity data streams, as they export the data and store it for later analysis making them less effective in dynamic and fast-moving threat environments.
Scalability
NetFlow analyzers which use simple database backends encounter run into scaling issues early on. They struggle to pack millions of flows into SQL databases while maintaining acceptable query times. This results in compromises such as flow rollups which keep only “raw flows” for a week and then only store large flows after that.
How Trisul Addresses These Challenges
Trisul’s game-changing technology not only addresses the limitations of legacy traffic monitoring solutions but also enhances monitoring, troubleshooting, and securing networks along with evolving network dynamics. Let’s explore how in the following,
Real-Time Network Traffic Analysis
Prioritizing real-time analysis is essential for any traffic monitoring tool. Trisul NetFlow Analyzer achieves this by leveraging Streaming analytics that process and analyze data in real time. Even more, unlike basic NetFlow analyzers that rely on a SQL-based flow database for long-term queries, Trisul streaming analytics process NetFlow data into precomputed traffic metrics and topper snapshots, which are treated as first-class objects. This approach enables efficient long-term queries for any of the 100+ metrics that Trisul provides out of the box.
Deduplication
In large networks, NetFlow data might be collected from different routers and switches resulting in multiple records for the same flow, or when capturing both ingress and egress flows from a network device, duplications can occur. These duplicate flow records may have varying time stamps but contain identical flow information. Trisul deploys deduplication algorithms that can identify duplicate flow records to enhance accuracy, accelerate analysis, and save storage space.
Multi-Tenancy
In complex networking infrastructures, meeting business requirements can be particularly challenging, especially for monitoring multiple disparate networks. Legacy tools prove impractically expensive as there would be redundant resource usage. Additionally, ensuring data isolation and security for each tenant would be more complex and prone to errors. In light of these concerns, Trisul deploys multi-tenancy, which includes separate retention policies and effective management of IP address overlaps across instances in the topology. This approach ensures efficient resource usage, robust data isolation, and enhanced security.
Incorporating ML
Apart from real-time alerts triggered when thresholds are exceeded, certain performance-based alerts require analysis of metrics over a period of time to detect outliers using precomputed algorithms. Trisul integrates Machine Learning to create Threshold Bands of metric usage and identify outliers, enabling the system to send bandwidth alerts based on thresholds. This process begins by analyzing the long-term history of metrics, including counter groups, keys, and meter IDs, to compute a typical range where these metrics are usually observed. This trained data automatically generates an alert upon detecting outliers. Trisul’s ML-driven outlier detection identifies performance issues at an early stage before they escalate and impact service delivery or user experience. Moreover, this ML model adapts to changes in network conditions and traffic patterns over time rendering its functionality reliable even as the network environment evolves.
Customizable Metering
Trisul NetFlow Analyzer took additional measures to offer specialized features for companies that have custom requirements. Such as UI point-and-click creation of custom metering that includes rule-based metrics, IP, App Groups, or other group-based metering, Segmentation such as metering traffic on a particular subnet separately, and so forth.
Extensibility via Trisul Apps
Every customer will have that one extra need that isn’t quite there in any boxed product. Trisul NetFlow Analyzer recognizes this and the result is Trisul Apps. These are freely available add-ons that enhance the product. Some popular apps are CIDR Flow Explorer, Sankey Charts, Super Search Hosts.
Geo
Geo plugin is one of the add-ons you can install on Trisul that helps you map IP addresses to their geo-locations. Trisul integrates geo location databases from Maxmind and IP2Loc that allow you to add country-wise traffic metering, ASN-wise metering, city/region-wise metering, IP prefix-wise metering, and BGP metrics for ISP applications.
Badfellas
Badfellas is a comprehensive threat detection plugin that checks your network traffic against millions of indicators to detect malicious activities. Your network traffic is scrutinized for matching IPs against blacklisted IPs, matching blacklisted domain names even if no response was received or hidden in DNS records, checks for blacklisted HTTP host, the Server Name Indicator (SNI) is inspected, and checks SHA1 fingerprint. Even more, you can also create custom indicators. Based on these detections automatic alerts are generated where you can get useful reports including the top 100 hosts with malware in your enterprise, infection trends over time, retrieve suspected malware flows, and more.
The Bottom Line
While Trisul is a unified platform for network data analytics and compliance, its true distinction lies in the innovative and meticulous efforts behind its development. Combining real-time analytics with advanced Machine Learning and efficient deduplication, Trisul provides unparalleled insights into network performance and security. Its customizable features and powerful plugins like Geo and Badfellas demonstrate a commitment to exceeding industry standards and transforming network data into strategic assets. Trisul empowers organizations to navigate the complexities of modern network environments with unmatched efficiency and effectiveness.
Related: Explore Top Reasons to choose Trisul NetFlow Analyzer
EXPLORE OUR PRODUCT PAGE FOR MORE INFO
Discover the Power of Trisul NetFlow Analyzer